Booting Linux from CD, in 2022
Yes, "CD", not USB, not network-boot, not DVD.
TL;DR
Ubuntu Oneiric ubuntu-11.10-desktop-i386.iso, at 695MB, is the newest 32-bit graphical Ubuntu live image that will fit on a 700MB CD-R.
If I was doing this again, I'd consider: Puppy Linux, far more up-to-date, supports 32-bit, fits on a CD, can choose to be based off Debian packages.
Background
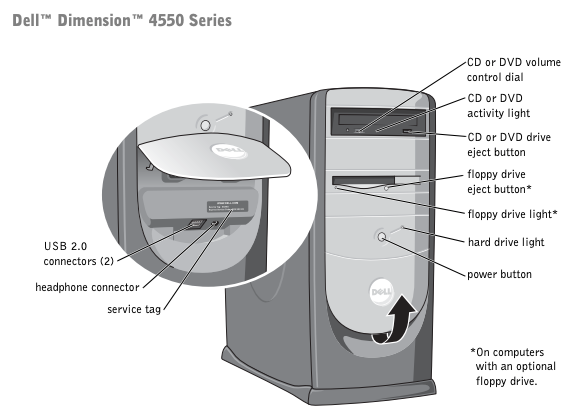
Recently, I had to extract some data from a 2002-era Dell Dimension 4550 desktop, running Windows XP Home edition, with a few password-protected user accounts, but no full-disk encryption.
The machine has USB ports, two 10/100 ethernet cards, DVD-RW drive, CD-RW drive, and a floppy drive.
The disk drive is parallel-ATA, so I don't have a handy external-hard-drive-case/USB adapter for it. So I had to boot the machine to get the data out.
Booting an entirely obsolete computer
Usually, booting is pretty straightforward: flash a USB drive to the latest Ubuntu live ISO, boot from USB, image the disk to network storage with dd, or even just cat, then mount the disk read-only to browse.
But this wasn't so easy - it got a bit ridiculous, and it dredged up some tricks I hadn't used for decades. I thought it might be fun to chronicle the challenges faced below.
Default Windows XP Admin Password
I tried logging in with the default empty-string hidden Windows XP Administrator account by pressing Ctrl-Alt-Delete twice at the login screen, then logging in as Administrator/"". Yes, Windows XP set up everyone up with an empty-string backdoor by default. 2001 was truly a wild-west time in computer security. However, the savvy previous owner had reset the password.
Resetting BIOS password
The boot device order was controlled by the BIOS password. To adjust this, I tried taking out the CMOS battery for a few seconds (amazing that these batteries still work, so many years later), but the password remained. I looked up the manual, and reset the BIOS password by moving the jumper on the motherboard, booting, then resetting the jumper, and rebooting, which worked.
Booting from USB
I tried booting from 2 different flash drives, but the BIOS wouldn't recognise either. Wouldn't even show them in the boot selector. This was very disheartening, considering the manual says it can boot from USB!
Booting from the network
I'd never network booted before. I figured, instead of burning some optical media, let's learn a new skill.
I heard good things online about netboot.xyz, a skeleton iPXE network boot image that can download ISOs from the internet, then boot into those ISOs. I set up our home Synology NAS with a TFTP server hosting netboot.xyz.kpxe, testing it by running tftp <synology ip address>, and set up the Unifi DHCP server to respond to DHCP requests with the Synology's IP address and filename. However, the Dell kept erroring with PXE-E53: No boot filename received. The DHCP response is a broadcast; so I can see the DHCP response from Wireshark on my laptop, and the boot filename was definitely present in the packet. I don't know what was going wrong here, but I gave up on it.
Booting from DVDs
I really didn't want to start burning DVDs (like everyone else... I haven't burned a disc in over a decade), but I was running out of options. I tried booting the newest Ubuntu from a DVD-R, that failed because Ubuntu has dropped support for i386, now only offering x64. kali-linux-2021.4a-live-i386.iso (3.17GB) is a 32-bit image, but froze on startup. I burned through many DVD-Rs and DVD-RWs before concluding the computer's DVD drive, or burner, is probably corrupting data, or perhaps is just unhappy booting from DVD-RWs.
Booting from the network, via CD
I burned netboot.xyz.iso to a CD-R and booted from that. But it kept hanging while downloading the image from GitHub. And even if it succeeded, it would have taken an unreasonably long time to download. Maybe the TCP stack on these images isn't too great? Or maybe the 20-year old CD drive is corrupting data? Hard to know.
Booting from CD
I tried Clonezilla Live clonezilla-live-2.8.0-27-i686.iso, a Linux Live CD that images hard drives to a network location (kind of a Linux version of Norton Ghost). But it kept locking up in the middle of the transfer. Felt very unreliable.
I tried burning debian-11.2.0-i386-netinst.iso (492MB) to a CD. And it booted nicely! But true to its name, it's just a network-installer, it doesn't offer a live environment, only a minimal terminal, lacking the tools needed for disk imaging. It's not designed as a Live CD and doesn't operate as one.
Booting from USB, via CD
I tried plopkexec, a very small boot image containing USB and filesystem drivers, that you can burn to a CD, boot from, and load data from a USB drive, and launch the OS from. I thought this might be a good way to workaround the BIOS's lack of support for booting from USB. It's named for the kexec function, a relatively new addition to Linux, which is like execve, but for switching kernel binaries rather than switching userland binaries. plopkexec was able to detect my USB disk, and the partitions within, and start booting from them, even executing the kexec to switch into the USB's kernel, but then failed because I wasn't passing the right arguments to the new kernel. It seems these options are typically set by GRUB, and GRUB has a configuration file language that plopkexec can't parse. I tried passing the args using plop's UI, but had no further success.
Booting from an ancient Ubuntu CD
Pretty much defeated, I fell back to the backup plan: run an 11-year-old version of Ubuntu that can fit on a CD.
Although Ubuntu has turned down the update servers for old versions (so no apt-get update for you), they still host the Live CD ISOs at old-releases.ubuntu.com. The newest version that fit on a CD was 11.10 Oneiric (from October 2011!).
This booted up nicely, dropping me into a familiar graphical shell with the usual optical media lag whenever you click anything.
I tried imaging the disk with cat /dev/sda | ssh user@synology:/dell/sda.img but hilariously, the Synology and Ubuntu couldn't agree on any hash algorithms; I suppose all the eleven-year-old hashes have been compromised/deprecated?
In the end, I imaged the disk with raw TCP, using good old Netcat: on the Synology, listening on TCP port 10000 with $ nc -l 10000 > /dell/sda.img, and on Ubuntu, sending the disk image with $ cat /dev/sda | nc synology 10000.
Aside: cat seems to work fine for imaging a disk. The community seems to have this weird cultural attachment to using dd for imaging disks, presumably so you can set the block size to optimize reads? But in my experience, Linux kernels can saturate the disk with the default block size of cat, maybe they're smart enough to do read-ahead? Or maybe everyone's copy-pasting the wrong block size for dd. Anyway, cat is a bit easier for me to understand, so I used cat. Real pros could probably use shell input redirection direct to netcat, but whatever, this isn't CPU-bound.
Resetting Windows Passwords
Having imaged the disk, it was finally time to reset the Windows passwords, by editing the registry files, with chntpw. I burned the 18MB image to another CD-R, booted successfully, and overwrote all the user passwords with empty-string.
Booting into Windows XP
I rebooted the machine into Windows XP, logged into a user, and stepped into a distant past, where Firefox isn't able to talk to most web servers because most of the server's ciphersuites have been updated. Google served me up with a fallback mobile experience.
I recovered some ancient saved passwords using NirSoft's Windows Password Recovery Tools.
Mission accomplished
I'd expected some trouble booting this... but not as much as I got. In retrospect, I should have just booted off an old Ubuntu CD much earlier, I was worried about running such old software, but it just worked.
I didn't expect OpenSSH/TLS ciphersuite/hash-function negotiation to be such a problem that computers couldn't talk to each other, over just 11 years.
I hope this is the last time I ever have to boot from optical media! At least I didn't have to boot from floppy disk :-)



Comments ()